Exagrid Directory Traversal Vulnerability (CVE-2019-12310) to “Support” Credential Extraction
Summary
The Exagrid backup appliance at version 4.8.1.1044.P50 suffers from a directory traversal vulnerability at “http://EXAGRID_IP/monitor/data/Upgrade/” (case sensitive) which allows unauthenticated access to detailed log files. Active “support” credentials were found within these logs in Base64 encoded format.
The credentials were confirmed as used to facilitate upgrades on the appliance through a series of Perl scripts. The execution of one such script dumps the encoded credentials into the log file “progress.log” within this directory. These ‘support’ credentials allow for administrative level access to the appliance and its data once decoded.
Credit
This vulnerability was identified by Jeremy Trinka, Senior Security Engineer with InquisIT.
Identification
The Exagrid appliance maintains a “support” account for use by support to perform upgrades of the appliance, as well as to run maintenance tasks. The credentials provide access to data on the appliance at an administrative level, which makes the vulnerability significant.
The web content scanning tool ‘DIRB’ was run against the Exagrid web console to identify open directories. The scan resulted in the positive identification of the URL “http://EXAGRID_IP/monitor/data/Upgrade/” (case sensitive).
When browsing to the directory, the appliance presents the below accessible files.
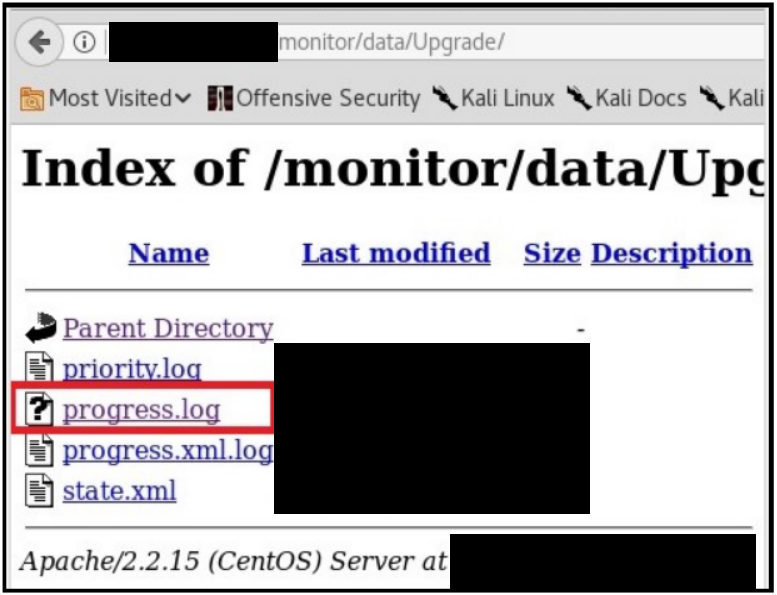
Attention was directed to the “progress.log” file, which was found to contain verbose upgrade process information. The file identifies output from a Perl script “upgradePart2.pl” which was executed with Base64 credentials on an “–EncodedLogin” argument.

The value was then decoded, and found to contain the “support” username and password pair. These credentials were verified by accessing the web console of the appliance.

Considering the unauthenticated and remote nature of this vulnerability, it can be easily scripted to automate the extraction of encoded credentials.
Impact
Significant — The process above was tested on multiple Exagrid systems, and found to be reliable in identifying administrative ‘support’ credentials on appliances which were upgraded to the affected version.
Mitigation
The issue was responsibly disclosed to Exagrid, and confirmation was received that a future release would address the issue. Users should contact their support representatives for information on updates. Credentials found using this process can be reset with the assistance of support.
Disclosure Timeline
- 7/10/2018 – The vulnerability was identified, and Exagrid support was contacted with the details.
- 7/13/2018 – Exagrid support confirmed the issue and it’s intent to resolve it in a future release.
- 7/19/2018 – Final communication from Exagrid. No further information was received by the vendor.
- 5/23/2019 – Disclosure of vulnerability to MITRE for CVE numbering reservation.
- 6/4/2019 – CVE ranked and published. MITRE, NVD